Protect your FIDO enabled online accounts with Key-ID U2F keys
Usernames and passwords are not enough.
Facebook, LinkedIn, Yahoo and Dropbox data breaches have all been big news stories, but these high visibility cases lead to criminals accessing many other accounts, where the victims have used the same or similar usernames and passwords. Password management services try to help people cope with the multitude of unique passwords required for each of their account log-ins, but some of these too have been the victim of hackers1. Criminals are also making use of the malware that routinely finds its way on to phones, tablets and laptops to steal passwords, as well as tricking people into revealing their sign-in details through increasingly believable phishing scams. The reality is – relying on only usernames and passwords is not secure enough today.
So what’s the best solution?
Experts agree that two-factor authentication that relies on some unique physical thing that you own, in addition to some secret (password or PIN) that you know, provides far greater security. SMS is no longer recommend as an additional means of account security, because it has been found to be easily bypassed by hackers.
The FIDO (Fast Identity Online) Alliance has created a universal open standard for two-factor authentication (U2F), making it possible for different online services to be secured by the same physical U2F key. This makes it easy for people to activate strong two-factor secure account sign-in because they are able to use the same physical key for many services. Unlike using the same password for different accounts, it’s fine to use the same U2F key because the key secretly generates unique codes for use with each specific account it’s registered to, without ever sharing its own private cryptographic key. Also, a lost key cannot be misused to reveal the identity of its owner because no personal information is linked to the key itself.
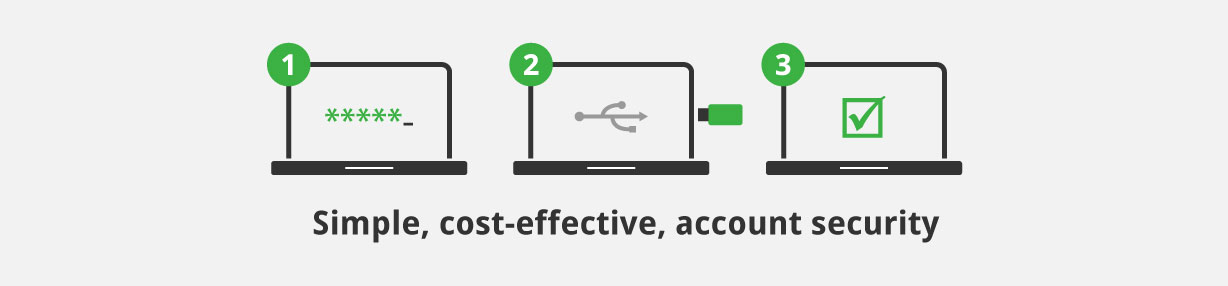
Account hijacking can be stopped in its tracks with FIDO standard U2F keys – simply register one of these hardware keys with all your compatible online accounts. The many online services that support U2F keys can be set up to require your key to be used whenever sign-in is attempted from a new device, so it won’t get in the way of day-to-day usage, but you have the peace of mind that stolen login information alone will not allow anyone else access to your protected accounts.
U2F keys are better than other forms of two-factor authentication in guarding against the threat of look-a-like phishing sites that try to trick people in to giving up their log-in information. ‘Time-of-use’ phishing attacks can capture other 2-step authentication responses (including OTP codes) and immediately relaying these on, under the control of hackers, to give inappropriate access. The highly secure way in which U2F keys are used to establish, and mutually verify, a connection with the account servers effectively eliminates phishing threats. A FIDO U2F key will only work with the sites it’s supposed to, and stolen usernames and passwords alone will not be enough to gain access to FIDO-enabled accounts.