Securing G Suite access
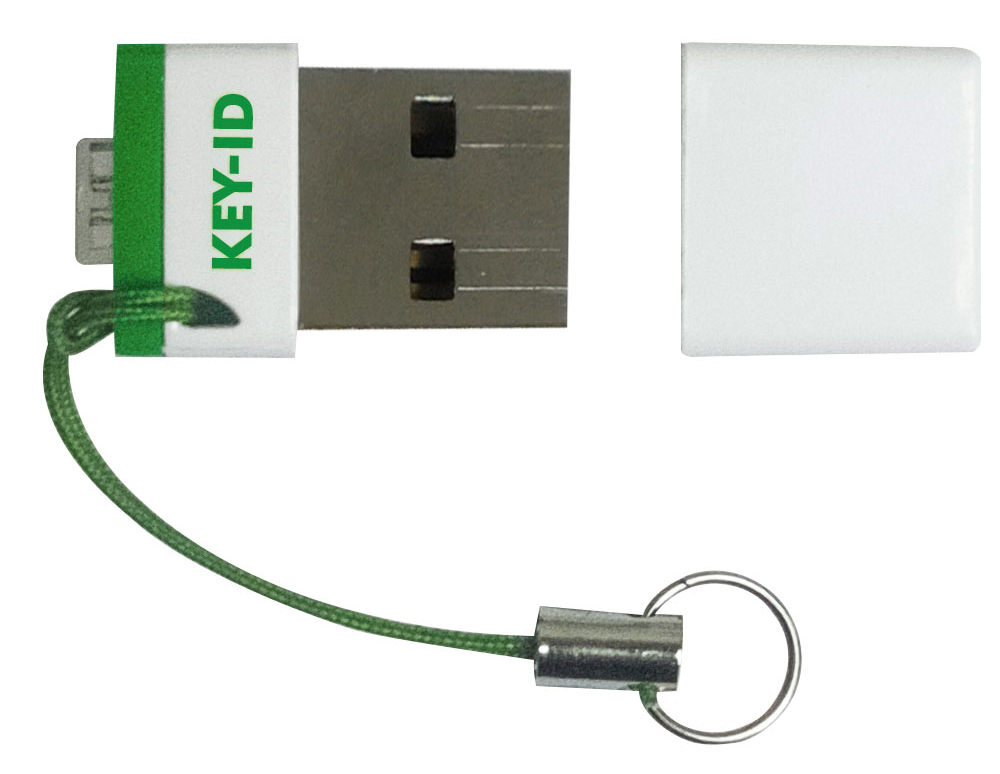
Use a single, cost-effective U2F token

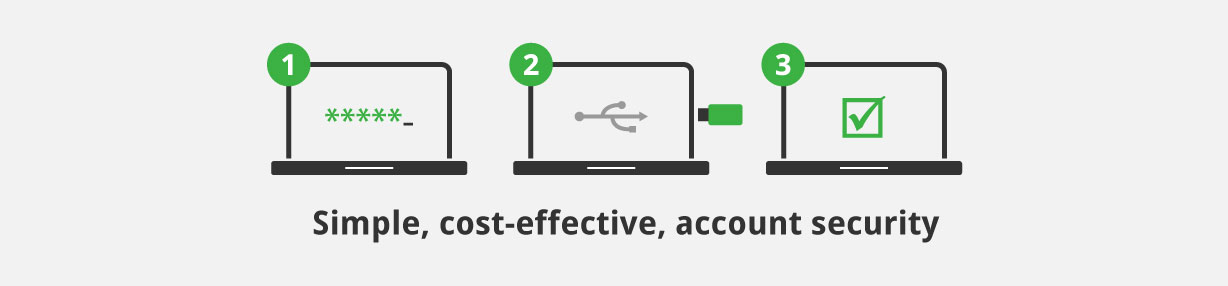
Easy to deploy, simple to use, physical 2nd factor security
G Suite Enterprise allows admins to make 2-Step Verification work only with U2F security keys. Not allowing other less secure forms of 2nd factor identity verification improves overall security. Google recommends that 2-Step verification should always be enabled and enforced for all user accounts.
Easy to deploy
Enable two factor authentication for your domain in your Google Admin console.
Users can then self-register their keys. Admins can set an ‘enforcement from’ date, to give users some time to register their keys; each time they log-in they will be reminded and they will also receive reminder emails until they enrol. From the chosen enforcement date, users who have not yet enrolled will be required to enrol before they can log-in.
That’s it! Stronger security, greater user convenience and easy deployment.
Simple to use
When signing-in to G Suite users are prompted to insert their FIDO key into a USB slot and press the button. That’s it!
No drivers or software to install for FIDO U2F compatible browsers: Chrome and Opera.
No manual typing of random codes or need for a mobile phone or SMS messaging.
The same key can also be used to secure account access to other FIDO complaint online services, such as Dropbox and Salesforce.com. Attaching the U2F key to a keyring ensures it’s always on hand when needed.
“Protecting our G Suite information from phishing attacks has been straight-forward and economical with Key-ID U2F keys”
Mr Marc Ginnaw
IT Manager
The Angmering School, Brighton, UK.
Why 2 factor security?
Usernames and passwords just aren’t enough; known data breaches have impacted hundreds of millions of accounts while new phishing and man-in-the-middle threats are emerging all the time. FIDO U2F authentication provides far greater account protection by requiring the additional verification of a unique physical key that uses highly secure embedded public key cryptography, making them effective against ‘time-of-use‘ phishing attacks which can capture other 2-step authentication responses (including OTP codes).
Key-ID U2F keys available with volume pricing from SmartcardFocus.com